Tool Search: Login Security Settings
The Login Security Settings tool allows you to control whether or not Staff users will receive login alert notification emails and require multi-factor verification via an emailed code or authentication application.
For more information about tracking login notifications, see the Enabling Login Alert Notifications Emails of the Managing User Account Passwords article.
Only users with a Student Information System (SIS) Product Security role can access and modify values in the Login Security Settings tool.
Only System Administrators should have access to the Login Security Settings tool.
New Device Notification Settings
These settings determine whether or not users will receive an alert when logging into Infinite Campus using a new device (a device that has not been previously used to log into Infinite Campus using their credentials).
Do Not Send Login Alerts
To disable login notification emails, select the Do not send login alerts radio button (Image 2) and click the Save icon. Users will no longer receive an email each time their Campus account is accessed via a new or unrecognized device/computer.
Infinite Campus highly recommends using at LEAST the 'Send an alert when logging in with a new device' setting.
This setting does not apply to Student and Parent Portal accounts.

Image 2: Turning Off Login Alert Notification Emails
Send an Alert When Logging in with a New Device
To enable login alert notification emails, select the Send an alert when logging into a new device radio button (Image 3).
Login notifications will increase email traffic. Therefore, it is important to have adequate email capacity when enabling and using login alert functionality.
This setting does not apply to Student and Parent Portal accounts.

Image 3: Turning On Login Alert Notification Emails
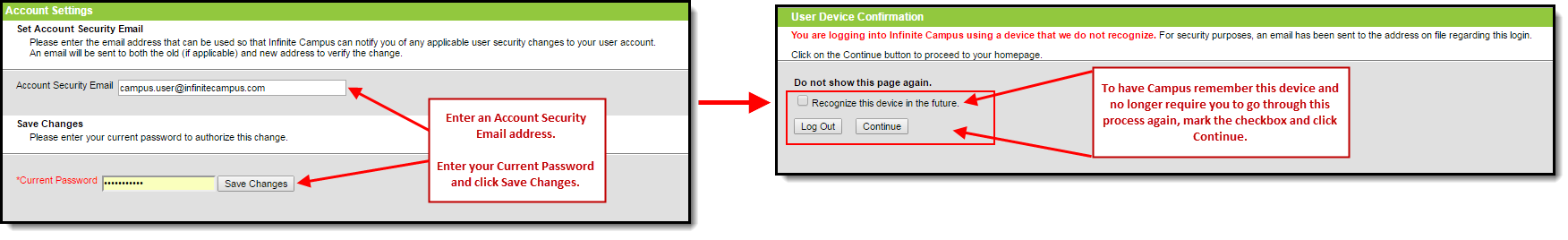
Once the Send an alert when logging into a new device radio button is enabled, users logging into Infinite Campus for the first time from a device will be required to enter an Account Security Email address (if one is not already present within Infinite Campus) and will be asked if they would like the device to be remembered for future logins (Image 4).
If email is not properly configured for your district, users may skip the Account Security Email verification process to avoid being locked out of Infinite Campus.
In order to properly receive security validation emails, your district needs to have a functional email relay configured within Email Settings.
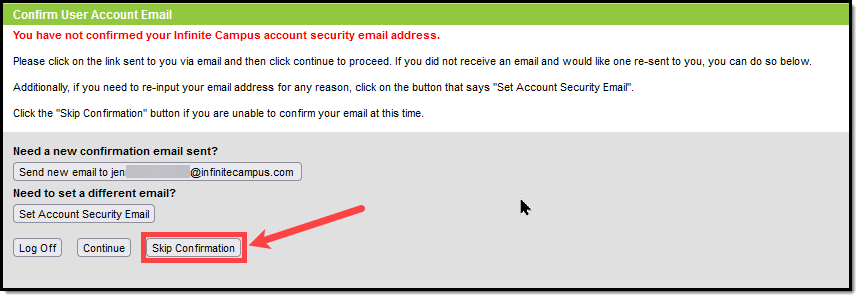
Image 4: Entering an Account Security Email and Remembering the Device
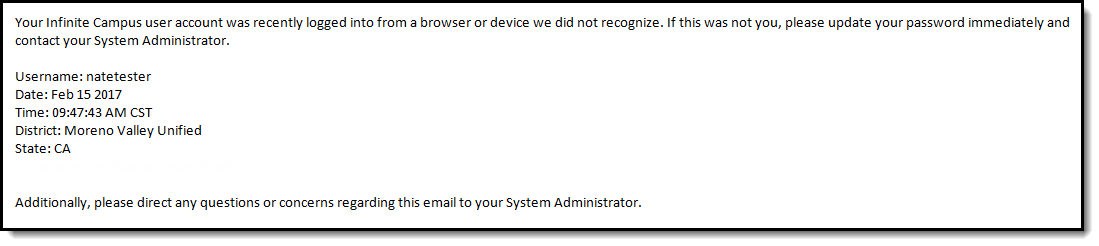
Once an email address is established, any time you log into Infinite Campus using a device that has not been used to log into Infinite Campus before or has not been designated as a device for Infinite Campus to remember will result in an email being sent to your Account Security Email address, alerting you that you (or someone) logged into Infinite Campus. Below is an example of the email you will receive (Image 5).
In order for a device to be recognized for future logins, your browser MUST be set to allow cookies.
Having your browser set to delete cookies automatically will cause the device to be unrecognized, forcing you to go through this process each time you log into Campus.
See the FAQ section below for more information about reducing the amount of notification emails that may be sent.
Image 5: Unknown Device Login Email Notification
Multi-Factor Authentication Options
These settings enable or disable multi-factor authentication and, if enabled, specify whether users authenticate via an email-based code or a third-party authentication app.
- Do Not Require a Verification Code to Log In
- Require Email-Based Multi-Factor Authentication Code
- Require Time-Based Multi-Factor Authentication from a Third Party App
Do Not Require a Verification Code to Log In
Select Do not require a verification code to log in to disable and do not require users to use multi-factor authentication when logging into Infinite Campus.

Require Email-Based Multi-Factor Authentication Code
To require users to enter a code emailed to them when logging into Infinite Campus:
- Click the Require Email-Based Multi-Factor Authentication Code radio button
- Set the frequency at which users must reauthenticate their credentials via email when logging into Infinite Campus.
- Each New Device - Users must reauthenticate each time they log in to Infinite Campus on a new, unrecognized device.
- Every 30 Minutes - Users who log out of Infinite Campus and attempt to log back in 30 minutes or more after their last login will be required to re-authenticate.
- Every Day - Users who log out of Infinite Campus and attempt to log back in 24 hours or more after their last login will be required to re-authenticate.
- Every Week - Users who log out of Infinite Campus and attempt to log back in 7 days or more after their last login will be required to re-authenticate.
- Every Month - Users who log out of Infinite Campus and attempt to log back in 1 month or more after their last login will be required to re-authenticate.
- To require email-based multi-factor authentication to apply to all SAML account logins, set the Require MFA for SAML Logins field to 'Yes'
- Select Save.
Login and verification code notifications will increase email traffic. It is important that you have adequate email capacity when enabling and using login alert and verification code functionality.
This setting does not apply to Student and Parent Portal accounts.

Image 7: Enabling Login Notifications with Verification Codes
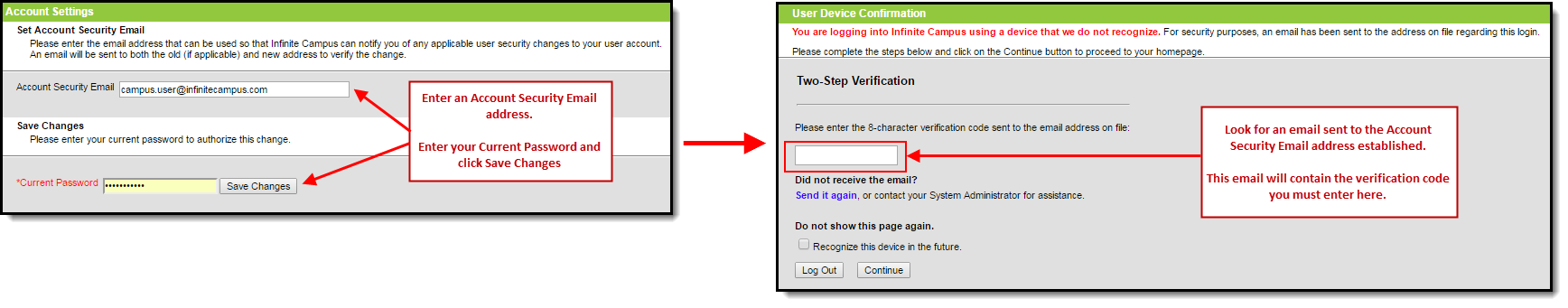
Once this setting is selected and saved, users logging into Infinite Campus for the first time from an unrecognized device must enter an Account Security Email address (if one is not already present within Infinite Campus). Once saved, they will be directed to a new screen where they must enter a verification code (sent to the email address entered in the previous step) and decide whether they would like the device to be remembered for future logins (Image 8).
For a device to be recognized for future logins, your browser MUST allow cookies.
Having your browser set to delete cookies automatically will cause the device to be unrecognized, forcing you to go through this process each time you log in to Infinite Campus.
Image 8: Entering an Account Security Email and Entering a Verification Code
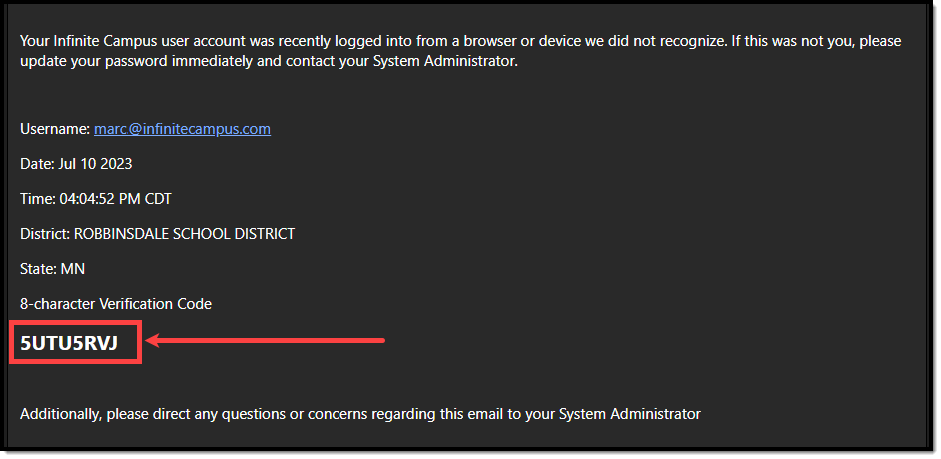
Below is an example of the email that will be sent to your account. This email contains the 8-character verification code that must be entered in the box shown above (Image 8).
This code expires after 20 minutes.
Image 9: Finding the Verification Code
Enter the 8-character verification code into the box shown below, decide whether to remember the device for future logins by marking the Recognize this device in the future checkbox, and click Continue (Image 10). The device is now verified; however, you may be required to reauthenticate, depending on the reauthentication frequency.
Image 10: Entering a Verification Code
Require Time-Based Multi-Factor Authentication from a Third Party App
User accounts can be enabled for time-based multi-factor authentication as an additional layer of protection for Infinite Campus accounts. When enabled, users are provided a unique QR code and Text Code, which requires them to authenticate their account using a device and an authenticator application (such as Google Authenticator, Authy, LastPass, etc.).

This setting does not apply to Student and Parent Portal accounts.
Time-based multi-factor authentication is required for all BIE user accounts and cannot be disabled.
If you experience any issues authenticating, know that your device must be in sync with the actual time in order to authenticate. Compare the time showing on your device to the actual time (https://www.time.gov). If the time on your device is out of sync, you can correct this in your device's Date & Time settings. In your device settings, you will likely find an option to enable automatic date and time syncing.
Alternatively, if you use Google Authenticator for Android, you can try the Time Sync feature (https://support.google.com/accounts/answer/2653433).
To enable device-based multi-factor authentication for all non-Campus Portal accounts:
- Click the Require Time-Based Multi-Factor Authentication from a Third Party App radio button
- Set the frequency at which users must reauthenticate their credentials when logging into Infinite Campus.
- Every New Device - Users must reauthenticate using an authentication application each time they log in to Infinite Campus on a new, unrecognized device.
- Every 30 Minutes - Users who log out of Infinite Campus and attempt to log back in 30 minutes or more after their last login will be required to reauthenticate using the authentication application.
- Every Day - Users who log out of Infinite Campus and attempt to log back in 24 hours or more after their last login will be required to reauthenticate using the authentication application.
- Every Week - Users who log out of Infinite Campus and attempt to log back in 7 days or more after their last login will be required to reauthenticate using the authentication application.
- Every Month - Users who log out of Infinite Campus and attempt to log back in 1 month or more after their last login will be required to reauthenticate using the authentication application.
- To require time-based multi-factor authentication to apply to all SAML account logins, set the Require MFA for SAML Logins field to 'Yes'
- Select Save.
Once enabled, the next time users attempt to log into Infinite Campus, they will see a screen displaying a unique QR Code and Text Code.
Using a device (such as a cell phone), users must download an authenticator app (such as Google Authenticator, Authy, LastPass, etc) and use the app to scan the QR Code or enter the Text Code. This will register the device and tie it to their Infinite Campus account.
Once they have scanned the QR Code or entered the Text Code in the authenticator app, the app will display a code. Enter the code from the authenticator app into the field on the Campus login screen, mark the Recognize this device in the future checkbox, and click Continue (see image below). The user will be logged into Campus.
Image 12: Registering a Device and Logging into Infinite Campus
In the future, when logging into Infinite Campus, depending on the reauthentication frequency set by the administrator, users will need to access their authenticator app on their registered device and enter the code displayed in the authenticator app into the field on the Infinite Campus login screen. Users should mark the Recognize this device in the future checkbox and click Continue. If the code they entered is correct, they will be logged into Campus.

Image 13: Logging into Infinite Campus Using an Authentication Code

Resetting a User's Multi-Factor Authentication Credentials
Tool Search: User Account Information
For districts using multi-factor authentication, selecting the Reset Account Settings button on their User Account will reset the user's multi-factor authentication configuration, requiring them to establish a new trusted device and log in using an Authentication app. See the Login Security Settings article for information about multi-factor authentication.

Captcha Settings
Captcha Settings determine which captcha is used on the Infinite Campus login screen for users who have failed to log in to Infinite Campus several times in a row. This feature prevents users from being locked out of their accounts after several failed login attempts and protects accounts from malicious bots and scripts.
These settings apply to Staff, Student, and Parent Portal accounts but do NOT apply to LDAP and SSO-authenticated user accounts.
The following captcha options are available:
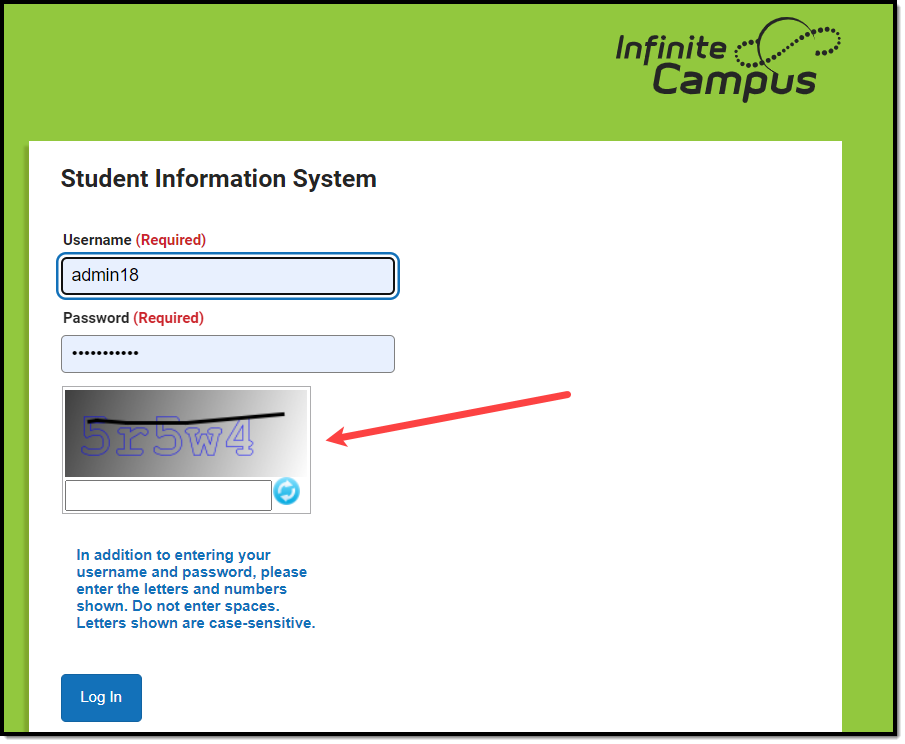
Campus Captcha
Campus captcha displays a captcha with a randomly generated set of letters and numbers that the user must enter in order to log into Infinite Campus.

Image 14: Enabling Campus Captcha
The image below is an example of the Campus captcha (Image 15).
Image 15: Example of the Campus Captcha
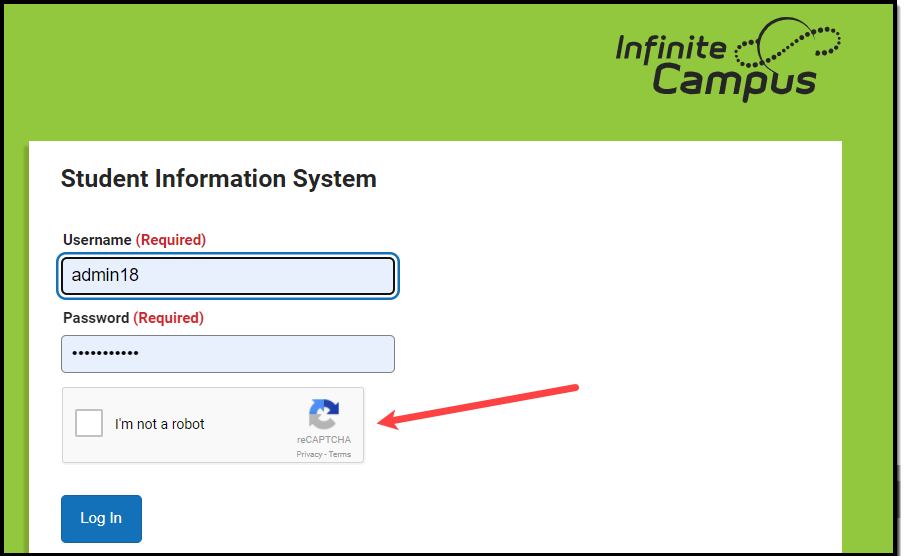
Google reCAPTCHA
The Google reCAPTCHA displays a checkbox that the user must click and a series of pictures that the user must select to prove they are human and not a bot.

Image 16: Setting Google reCaptcha Settings
Before enabling Google reCAPTCHA, you must register with Google to obtain the Site Key and Secret Key, then enter this data in Campus (Image 16).
See the Google reCAPTCHA website for more information about registration.
Campus only supports reCAPTCHA V2. You must use this option when connecting Campus to reCaptcha functionality.
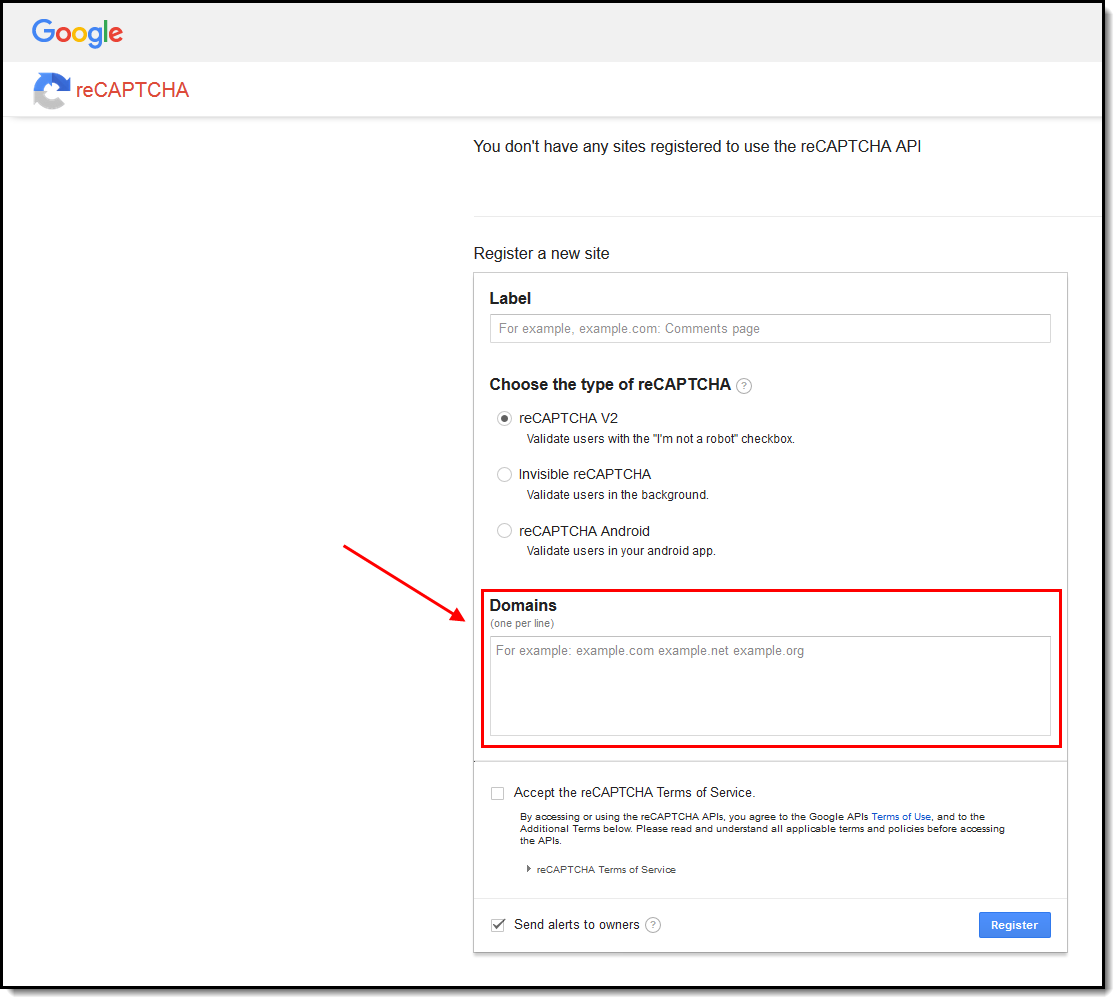 |
When registering for Google reCAPTCHA, enter the Domain by removing the http:// from the Campus site URL (for example, infinitecampus.org instead of http://infinitecampus.org). Do NOT enter the full URL. Failure to remove the http:// or https:// from the beginning of the URL will result in errors. |
Once Google reCAPTCHA is enabled, a user who has unsuccessfully attempted to log in to Campus several times in a row will be required to first check a checkbox (Image 17).
Image 17: Confirming You Are Not a Robot
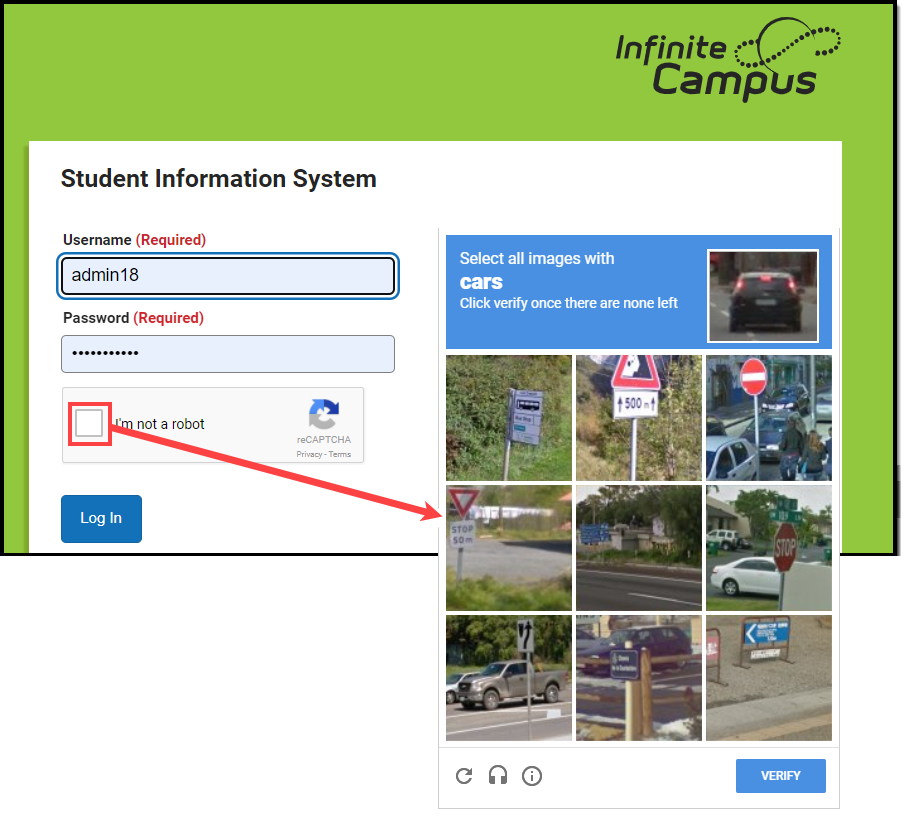
Once the user has marked the checkbox, reCAPTCHA will validate the user's behavior and return success if it believes the user is not a robot.
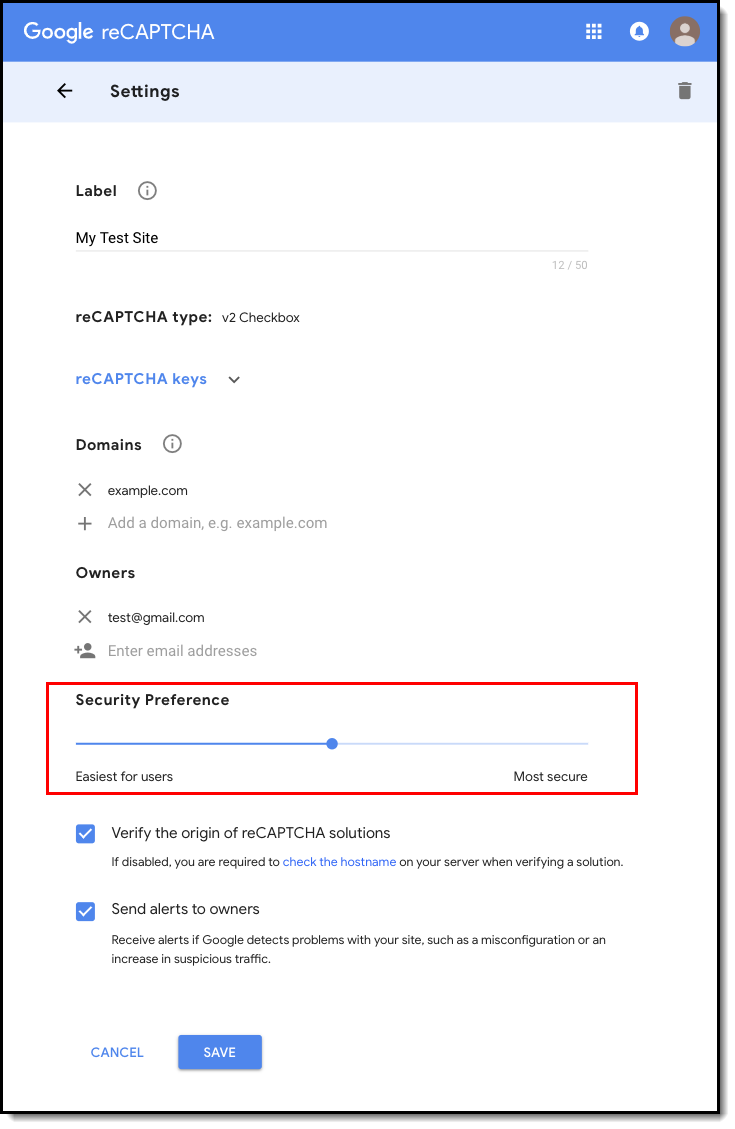 |
A Security Preference slider on the reCAPTCHA Settings screen allows for adjusting the security preference of the reCAPTCHA from 'Easiest for users' to 'Most secure'. This will determine the types of challenges generated by the captcha (i.e., easiest only requiring the I'm Not a Robot checkbox to be checked). |
Depending on the reCAPTCHA security preference level, a pop-up may appear, asking the user to select a series of squares or pictures based on a specific question (Image 18) or listen to an audio challenge.
The audio challenge option for Google reCAPTCHA does NOT work properly in Microsoft Edge.
Image 18: Selecting Verification Images
Once the user has successfully selected the correct images, they will be redirected to the Campus login screen, where they can log in to Campus.
If you experience any issues after setup, ensure the IP addresses Google requires for reCAPTCHA functionality are AllowListed. Google maintains its list of IP addresses that must be AllowListed in order for reCAPTCHA functionality to work here:
https://code.google.com/archive/p/recaptcha/wikis/FirewallsAndRecaptcha.wiki
For more information on troubleshooting other reCAPTCHA-related issues, see the Troubleshooting Google ReCaptcha article.
Enable Suspicious Login Attempts Mitigation
When the Enable Suspicious Login Attempts Mitigation setting is set to 'Yes', if 10 consecutive failed logins occur within a 5-second window, all users attempting to log in to Infinite Campus for the next 2 minutes are required to solve a CAPTCHA.

This setting applies to Staff, Student, and Parent Portal accounts but does NOT apply to LDAP and SSO-authenticated user accounts.
Infinite Campus HIGHLY recommends leaving this setting set to Yes as it provides a line of defense against automated attacks on your system.
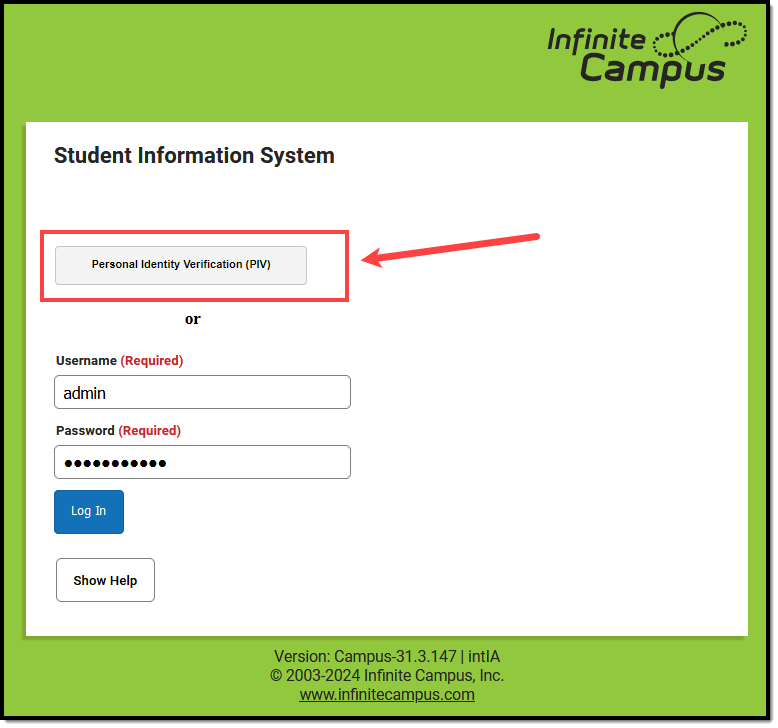
Enable PIV Authentication
The Enable PIV Authentication setting allows users to log in to Infinite Campus using a Personal Identity Verification (PIV) card.

PIV authentication only applies to Staff user accounts. This functionality does not affect Campus Student/Parent Portal accounts.
For a walkthrough of the PIV Authentication registration process, see the following articles:
- Administrators: PIV Card Registration Process for Administrators
- Staff Members: PIV Card Registration Process for Staff Members
When set to ‘Yes’, a PIV Card Authentication field is available on a person's User Account tab.
If enabled on the User Account, the Personal Identity Verification (PIV) button is made available on the Infinite Campus login screen. This button allows users to register their PIV card. Once approved, they can insert their PIV card into a card reader and select this button to log in to Infinite Campus instantly.
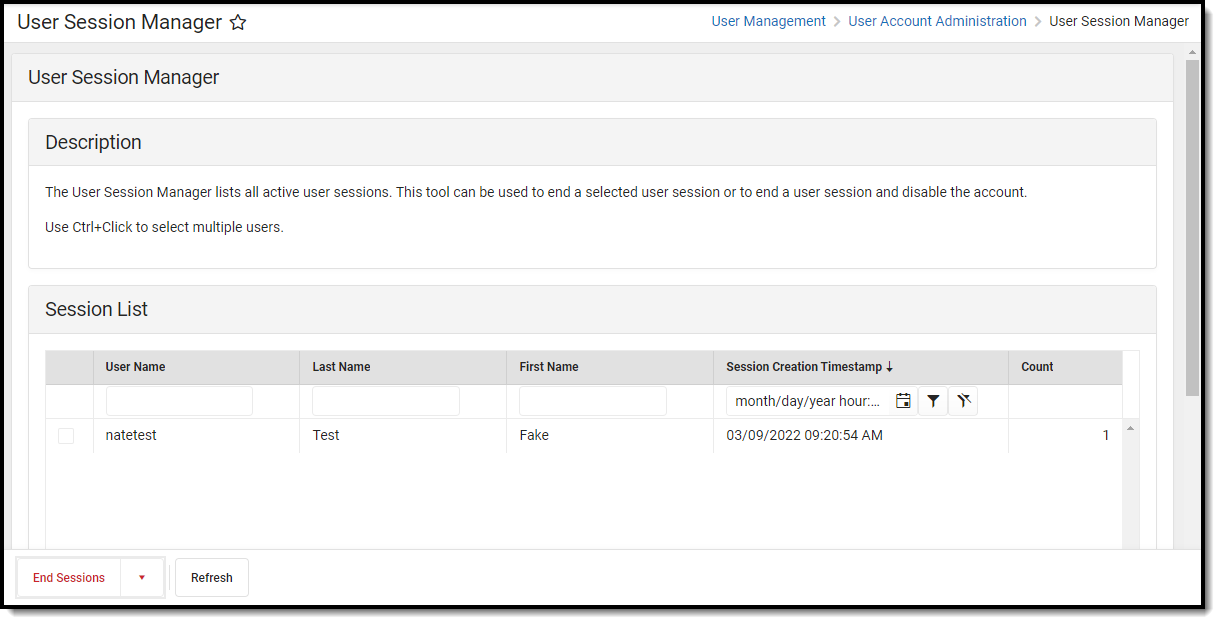
View All Active Sessions and Log Out/Disable User Accounts
Administrators can view a list of all active sessions within their instance of Infinite Campus and instantly log out or even disable specific user accounts via the User Session Manager. See the User Session Manager article for more information.
FAQ
Below is a list of answers to questions that may arise when enabling account notifications and verification codes.
- How Does Campus Remember a Device?
- What if I Clear My Cookies Each Time I Close My Browser?
- How Do I Minimize the Amount of Notification Emails?
- Will the Login as User Feature Result in a Notification Email?
- How Do I Reset a User's Account Security Email Address?
- Why Can't I Get reCaptcha to Work?
- Do Login Security Settings Apply to Both Staff and Student/Parent Accounts?
How Does Campus Remember a Device?
Once you log in to Campus, a unique ID is generated and stored as a cookie in your browser.
If you clear your browser's cookies or do not mark the Have Infinite Campus remember this device/browser in the future checkbox, you will have to go through the Notification process each time you log in to Campus.
For help in troubleshooting why your cookies keep being cleared, see the Troubleshooting Cookie Deletion article.
What if I Clear My Cookies Each Time I Close My Browser?
Clearing your browser cookies will remove the device from being remembered by the Campus notification process and will require you to enter an email and set up the device as a remembered device each and every time you log into Campus.
It is highly recommended that you do not set your browser to delete cookies automatically to prevent the notification process from repeating each time you log into Campus.
For help in troubleshooting why your cookies keep being cleared, see the Troubleshooting Cookie Deletion article.
How Do I Minimize the Amount of Notification Emails?
You can minimize the amount of notification emails you receive by:
- Marking the Have Infinite Campus remember this device/browser in the future checkbox when logging in with a device.
- Ensure your browser does not automatically delete cookies.
- Reducing the number of times you log in to Campus on a public computer (since you would NOT want to mark the device as a remembered device).
- Turning off all Campus account login notifications by selecting the Do not send login alerts radio button

Will the Login as User Feature Result in a Notification Email?
Using the Login as User feature on the User Account tab will not send a notification to the person you are logging in as. Login notifications occur only when logging in via the Campus login screen.
How Do I Reset a User's Account Security Email Address?
If a user has accidentally entered an incorrect Account Security Email and thus cannot access the verification code email, you can reset the user's email address by going to System Administration > User Security > Users > User Account and clicking the Reset Account Settings button (see image below). Once selected, the user will be forced to go through the initial Account Security Email login process again.

Why Can't I Get reCAPTCHA to Work?
If you experience any issues after connecting Campus to reCAPTCHA, ensure the IP addresses Google requires for reCAPTCHA functionality are AllowListed. Google maintains its list of IP addresses that must be AllowListed here:
Do Login Security Settings Apply to Both Staff and Student/Parent Accounts?
The following Login Security Settings only apply to Staff user accounts:
These settings apply to LDAP and SSO-authenticated user accounts.
- Do not send login alerts
- Send an alert when logging into a new device
- Do not require a verification code to log in
- Require Email-Based Multi-Factor Authentication Code
- RequireTime-Based Multi-Factor Authentication from a Third Party App
- Enable PIV Authentication
The following settings apply to Staff, Student, and Parent accounts:
These settings do NOT apply to LDAP and SSO-authenticated user accounts.
- Campus captcha
- Google reCaptcha
- Enable Suspicious Login Attempts Mitigation